Cybersecurity within the eSTAR framework has undergone significant transformation over the past several years. What began as a brief reference to the FDA’s guidance on cybersecurity has evolved into one of the most extensive and documentation-intensive sections of the submission. It is now highly structured, auditable, and increasingly aligned with international regulatory requirements.
At Harbor Labs, we are in constant collaboration with medical device manufacturers to support their regulatory submissions, helping our clients navigate changes to the eSTAR system and develop the corresponding cybersecurity documentation packages. Whether you are a regulatory professional preparing a 510(k) submission, an engineer responsible for cybersecurity documentation, or an executive assessing the impact on development timelines, the following document serves as a comprehensive reference for the history and evolution of eSTAR.
Note on Template Variants
The FDA maintains separate eSTAR templates for non-in vitro diagnostic (nIVD) and in vitro diagnostic (IVD) devices. The cybersecurity sections in both templates are identical; therefore, all updates described below apply equally to each.
Changes by version as of April 1, 2026:
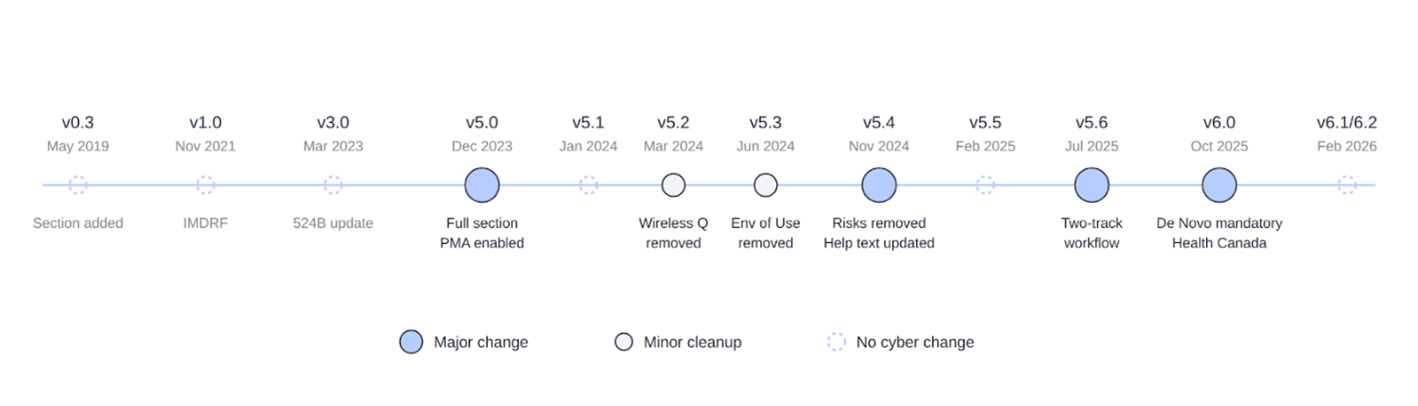
The cybersecurity section was initially introduced in version 0.3 (May 2019). In version 1.0 (November 2021), it was restructured to align with the International Medical Device Regulators Forum (IMDRF) submission framework, standardizing the organization of cybersecurity documentation across global regulatory bodies. In version 3.0 (March 2023), the help text was updated following congressional authorization granting the FDA authority to require cybersecurity documentation in premarket submissions.
Across these early versions, submitters were required to identify device attributes such as network connectivity, wireless communication capabilities, and external interfaces (e.g., USB ports), as well as to document cybersecurity risk management processes and associated plans.
Version 5.0 introduced a comprehensive cybersecurity guidance content framework. By this stage, the cybersecurity section expanded to include a fully structured documentation set spanning multiple pages, including:
- Risks question on unmitigated multi-patient harm or serious adverse events
- Security risk management report
- Threat model, including methodology and four required architectural views (global system, multi-patient harm, updateability/patchability, and security use case)
- Cybersecurity risk assessment using exploitability in place of probability for likelihood determination
- Software Bill of Materials (SBOM), including support levels and end-of-support dates for each component
- Safety and security vulnerability assessments
- Assessment of unresolved anomalies
- Cybersecurity metrics
- Security controls documentation with cross-referenced citations across eight categories
- Architectural views
- Cybersecurity testing documentation and reports
- Cybersecurity labeling references
- Cybersecurity management plan, including defined patching timelines

The eSTAR 5.0 interface introduced substantially more cybersecurity content requirements
The wireless function security question was removed from the Wireless Technology section due to redundancy with cybersecurity content.
No changes to cybersecurity requirements.
The Environment of Use subsection within the Wireless Technology section was removed, as it duplicated information already addressed in the cybersecurity section.
Three updates were implemented:
- Clarification that alternative approaches to FDA recommendations are acceptable if appropriately justified
- Removal of the question regarding unmitigated harm, as this evaluation is now reserved for FDA reviewers
- Revision of the Cybersecurity Management Plan help text to directly reference applicable guidance
No changes to cybersecurity requirements.
A streamlined workflow was introduced for device modifications. A single decision point determines the applicable documentation pathway:
- Cybersecurity impacted (or new device): Full documentation required, including threat modeling, risk assessment, SBOM, vulnerability assessments, architectural documentation, cybersecurity testing, security controls, and a cybersecurity management plan
- Cybersecurity unaffected: Reduced documentation set, including SBOM with component support status, vulnerability assessments, identification of uncontrolled risks, and a cybersecurity management plan

eSTAR 5.6 interface allowing for a device modification unaffected by cybersecurity to be reported
De Novo submissions were required to be submitted via eSTAR, making comprehensive cybersecurity documentation mandatory for novel device classifications. Additionally, Health Canada guidance text was incorporated throughout the template, facilitating parallel regulatory submissions.
No changes to cybersecurity requirements.
What was once a limited set of cybersecurity inputs has evolved into a comprehensive framework consisting of numerous required elements, including multiple attachments, structured questionnaires, and interdependent documentation artifacts spanning threat modeling, risk assessment, SBOM development, and security controls implementation.
The FDA has indicated that eSTAR will continue to expand to additional submission types, and cybersecurity requirements are expected to grow accordingly. Postmarket cybersecurity enforcement is also advancing, and future iterations of eSTAR will likely incorporate these expectations.
Manufacturers that align their cybersecurity programs with the current framework will be better positioned to adapt to future regulatory developments. Conversely, delayed adoption may result in increased effort and complexity over time.
Harbor Labs has been a leader in medical device cybersecurity since prior to the introduction of cybersecurity requirements within eSTAR. We have supported manufacturers across a wide range of device classes in developing complete cybersecurity documentation packages that meet FDA expectations without the need for additional information requests. Our eSTAR Cybersecurity Checklist maps each requirement to specific deliverables, ensuring completeness and efficiency. For organizations preparing upcoming submissions, further information is available at: https://www.harborlabs.com/contact




